Static Application
Security Testing
Analyze your source code for security vulnerabilities before they reach production. Our engine goes beyond simple pattern matching — it analyzes code structure, understands context, and uses AI to detect vulnerabilities that regex-based tools miss.
How Offensive360 SAST works
Parse & model your code
We build an abstract syntax tree and control-flow graph for each file, understanding how your code actually executes — not just what it looks like.
Analyze code paths
Our engine identifies how user-controlled input from entry points (HTTP parameters, form fields, API requests) reaches sensitive operations (database queries, file system access, command execution).
Apply security rules
We check against hundreds of security rules mapped to CWE IDs and OWASP categories. Each rule includes context about why the finding matters and how to fix it.
AI-enhanced detection
For complex patterns and supported languages, our AI engine analyzes code semantics to catch vulnerabilities that static rules cannot express — like business logic flaws and nuanced injection vectors.
{
"finding": {
"type": "SQL Injection",
"severity": "Critical",
"cwe": "CWE-89",
"file": "UserController.cs",
"line": 42,
"source": "Request.Query[\"id\"]",
"sink": "SqlCommand.Execute()",
"dataFlow": [
"Request.Query → userId",
"userId → query string concat",
"query → SqlCommand.CommandText",
"SqlCommand.Execute()"
],
"fix": "Use parameterized queries"
}
}Supported languages & frameworks
30+ languages covered. The broadest language support in the industry — more than Checkmarx, Veracode, or Fortify.
Built for security teams
A clean, actionable interface that helps your team prioritize and fix vulnerabilities fast.

Vulnerability statistics and trend analysis
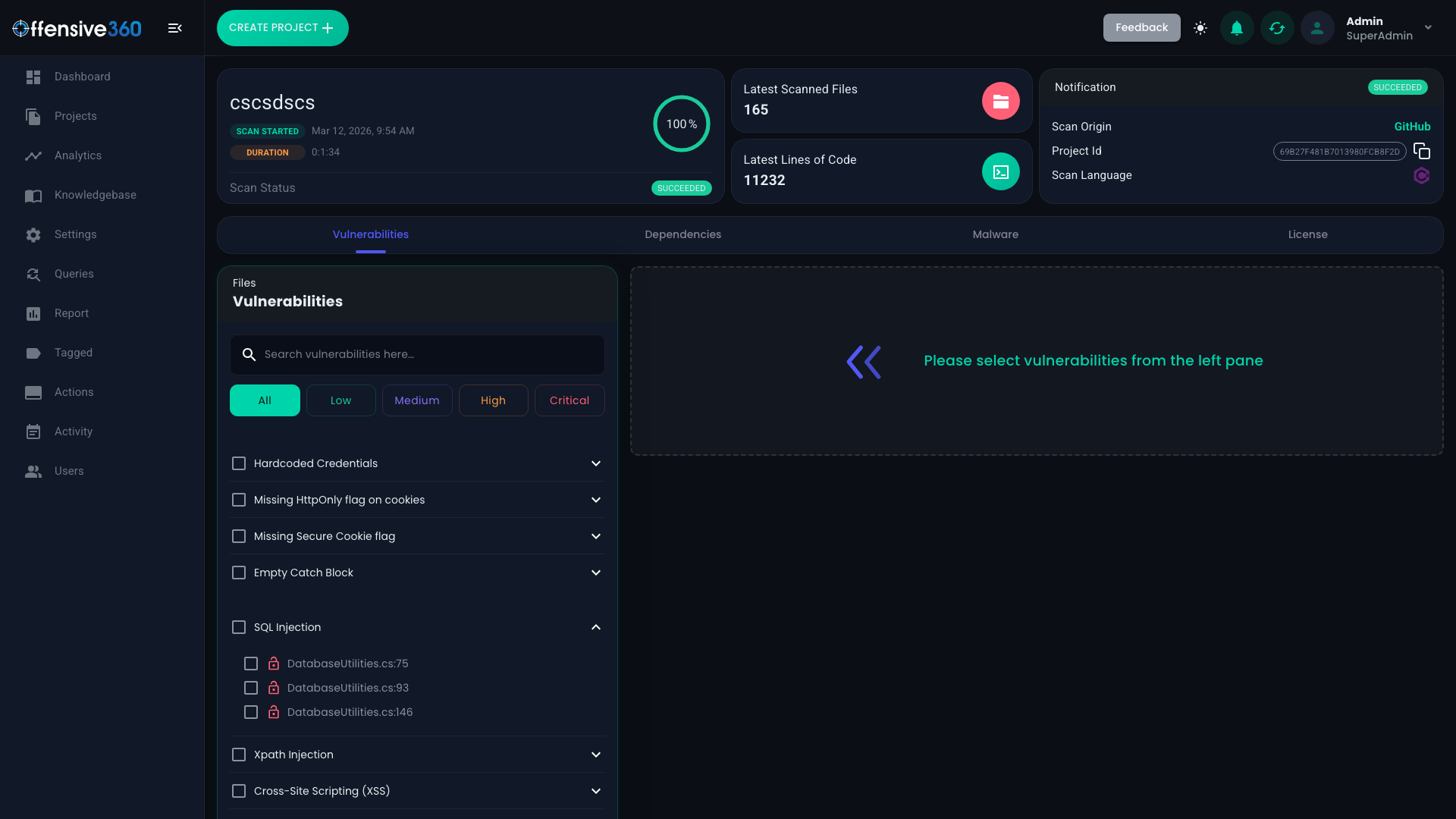
Detailed findings with code-level context
What we detect
Comprehensive coverage of OWASP Top 10, CWE Top 25, and hundreds of additional vulnerability patterns.
Scan your code now
Upload your project or connect your repository. Get your first SAST report in minutes.